What is purpose of using mysql_secure_installation?
Securing Your MySQL Installation: The Purpose of mysql_secure_installation
Understand why mysql_secure_installation is crucial for protecting your MySQL server from common vulnerabilities and how to use it effectively.
When setting up a new MySQL server, one of the most critical steps often overlooked by beginners is running the mysql_secure_installation script. This utility is designed to address several common security vulnerabilities that exist in default MySQL installations. Failing to run this script can leave your database exposed to unauthorized access and data breaches. This article will delve into the specific functions of mysql_secure_installation and explain why each step is vital for a robust database security posture.
Understanding Default MySQL Vulnerabilities
Out of the box, MySQL is configured for ease of use and broad compatibility, not necessarily for maximum security. This means certain settings are left in a state that could be exploited if not properly secured. For instance, a root user without a password, or a test database accessible to anyone, are common default configurations that pose significant risks. mysql_secure_installation systematically guides you through hardening these default settings.

Common default MySQL vulnerabilities before running mysql_secure_installation.
Key Security Enhancements Performed
The mysql_secure_installation script performs several vital security-related operations. Each step is designed to close a specific security loophole. Let's break down the primary actions it takes:
1. Setting a Strong Root Password
The most immediate and critical step is setting a strong password for the MySQL root user. By default, on many systems, the root user might not have a password, or it might be a well-known default. This step prompts you to create a robust password, which is essential for preventing unauthorized administrative access.
2. Removing Anonymous Users
MySQL often comes with anonymous user accounts that allow anyone to connect to the database without authentication. While convenient for testing, these accounts pose a severe security risk in a production environment. The script removes these anonymous users, ensuring all connections require proper credentials.
3. Disallowing Remote Root Login
By default, the root user might be able to connect from any host. This is extremely dangerous as it allows an attacker to gain full control over your database from a remote location if they compromise the root password. mysql_secure_installation restricts the root user to connect only from localhost, significantly reducing the attack surface.
4. Removing the 'test' Database
A database named test (and its associated privileges) is often created by default. This database is accessible to all users, making it a potential target for attackers to experiment with SQL injection or other exploits. The script removes this database and its privileges, eliminating an unnecessary risk.
5. Reloading Privilege Tables
After making changes to user accounts and privileges, it's crucial to reload the privilege tables to ensure the changes take effect immediately. The script handles this automatically, applying all security modifications without requiring a manual server restart.
root user. Avoid using common words, personal information, or easily guessable sequences. Consider using a password manager to generate and store complex passwords.How to Run mysql_secure_installation
Running the script is straightforward. After installing MySQL, you simply execute the command from your terminal. The script will then guide you through a series of prompts. Here's how you typically run it:
sudo mysql_secure_installation
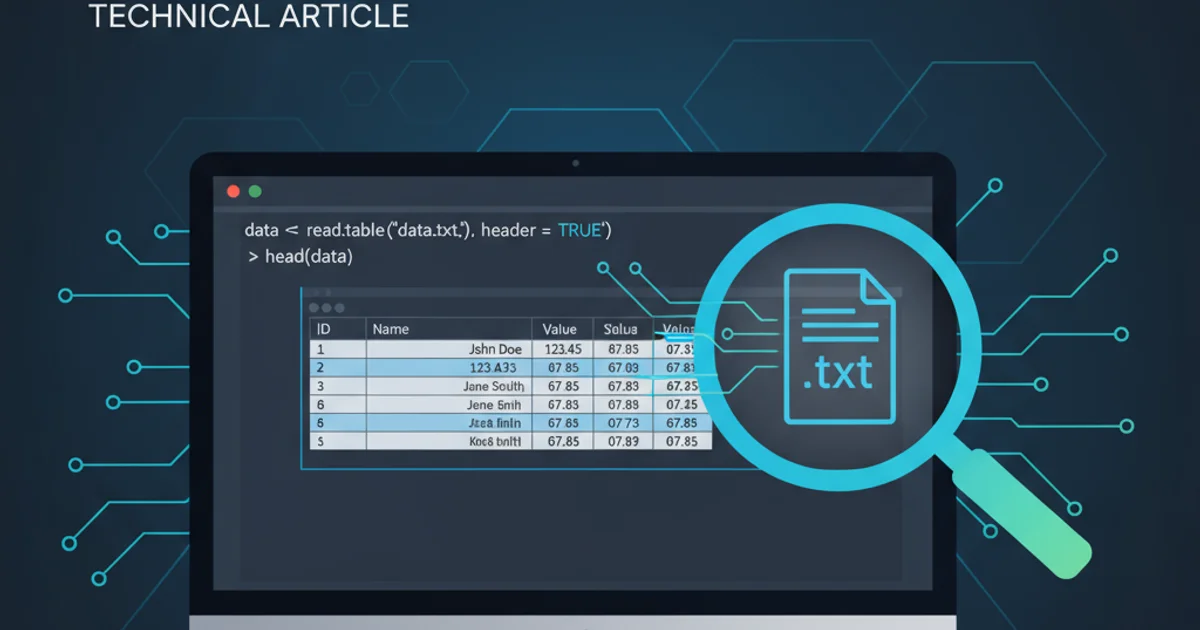
Executing the mysql_secure_installation script.
You will be prompted to enter the current password for the root user. If this is a fresh installation and no password has been set, you might just press Enter. Then, you'll be asked if you want to set a new root password, remove anonymous users, disallow remote root login, remove the test database, and reload privilege tables. It's highly recommended to answer 'Y' (Yes) to all these prompts.
root user is paramount. The root user is the ultimate administrator and its compromise means full control over your database.